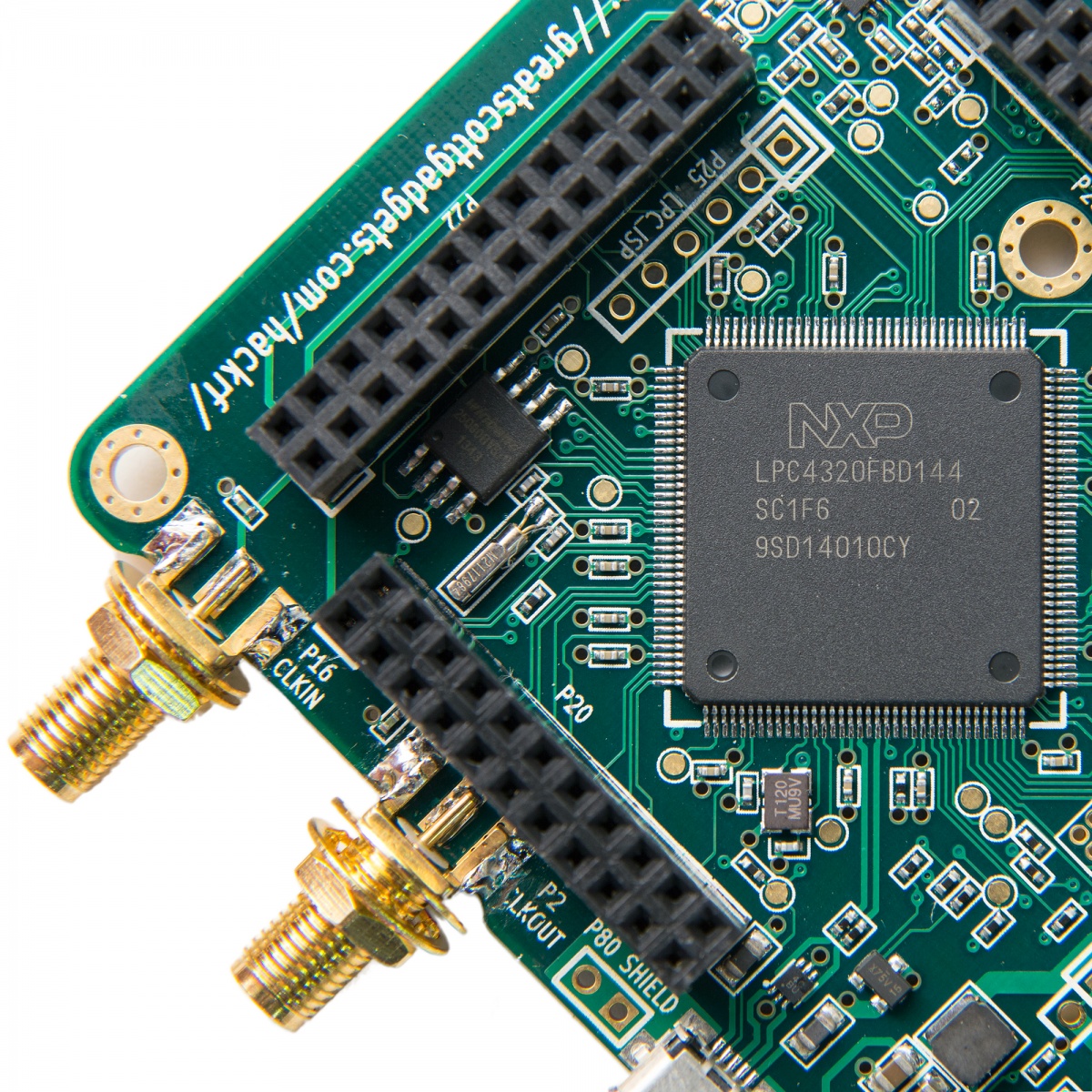
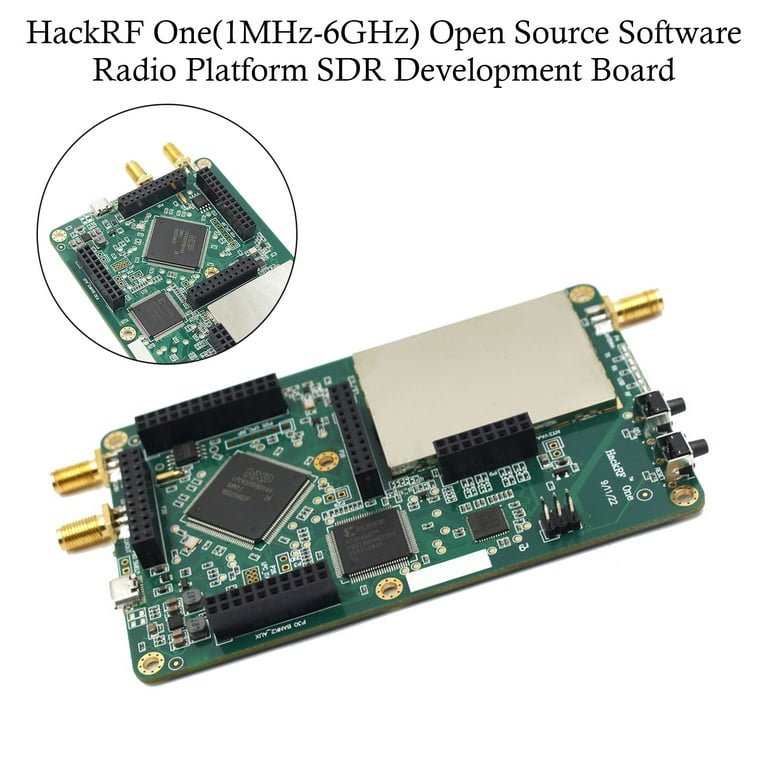
While performing a STIC evaluation of a product, the evaluation team at jtsec thought that it would be interesting to analyze the communications between two embedded devices that were part of the product. The main objective was to determine whether those communications were properly secured with encryption and other important security measures when it comes to devices that communicate using radio frequencies such as protection against jamming, GPS spoofing or replay attacks.

alvaro (@alvarontwrk) / X

2022 CC Statistics report: will this year beat last year's record

jtsec, Blog
alvaro (@alvarontwrk) / X

jtsec Blog about computer security, sharing jtsec thoughts

OpIcarus: A Success or Failure

jtsec, Blog

ICCC2023 Statistics Report, has Common Criteria reached its peak

ICCC2023 Statistics Report, has Common Criteria reached its peak

jtsec Beyond IT Security on X: The development of a patch

jtsec, Blog
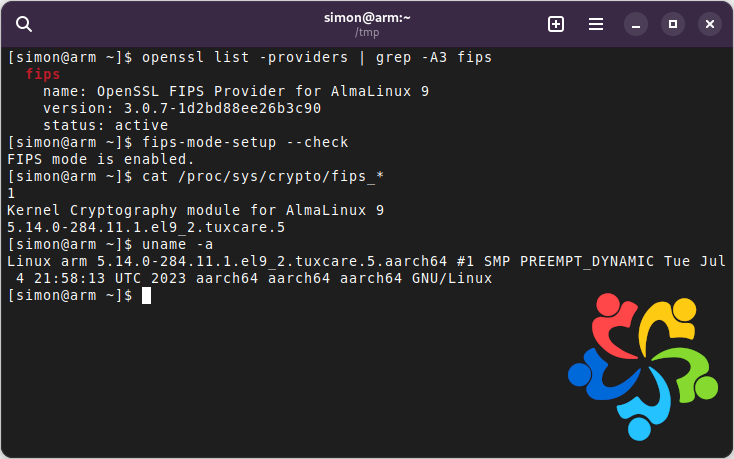
AlmaLinux OS - Forever-Free Enterprise-Grade Operating System

jtsec Beyond IT Security on LinkedIn: jtsec, Blog